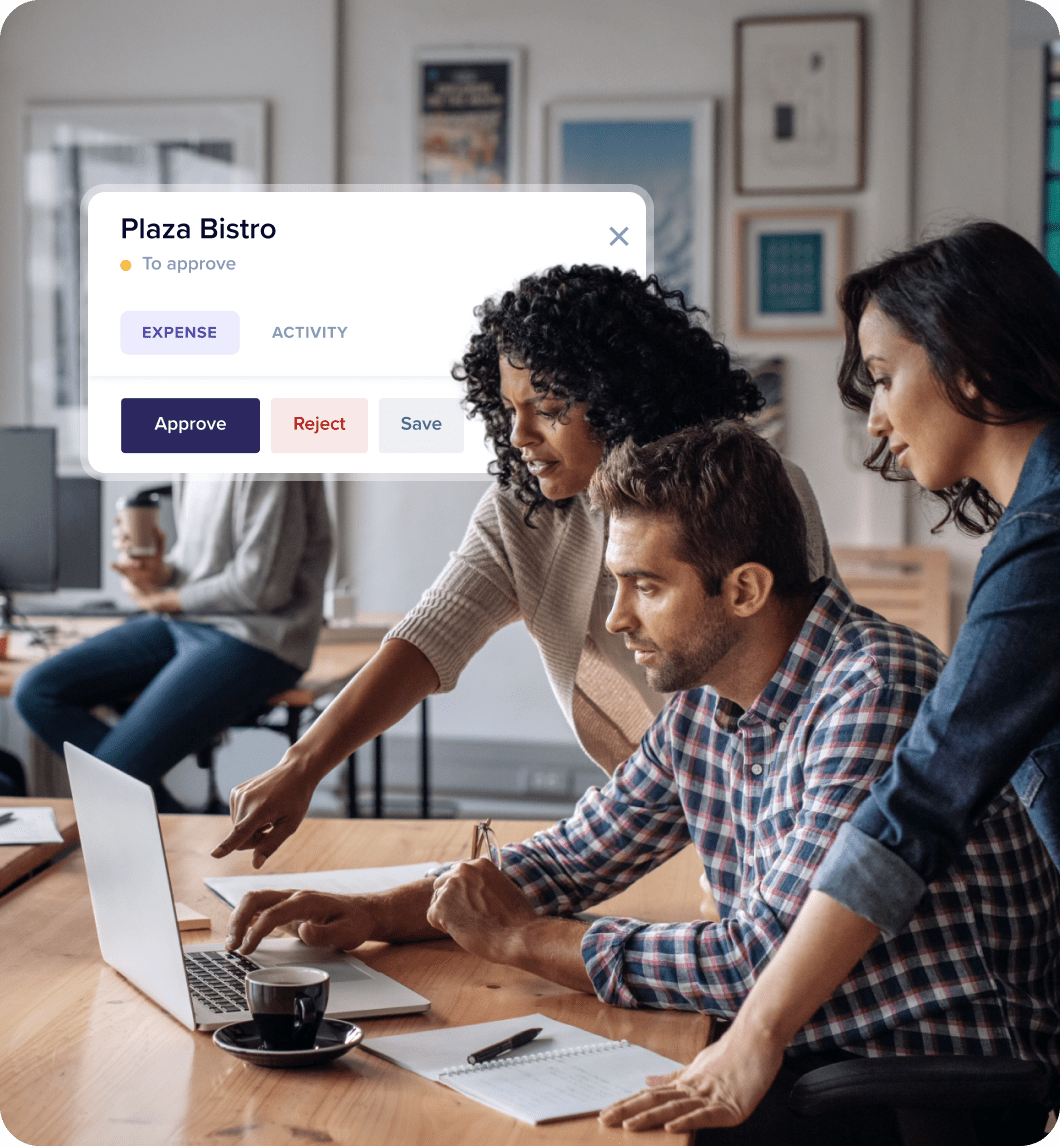
Smart expense management for efficient teams
Rydoo empowers finance teams to control employee spending, ensure local compliance, and increase efficiency by 3x.
Trusted by leaders and disrupters across 130+ countries
A smarter way to manage expenses
Why Rydoo?
Increase expensing efficiency
Submit and manage expenses effortlessly, in real-time and on the go.
Control employee spending
Get full visibility and control over employee spending, identify trends and anomalies, and respond promptly.
Ensure local compliance
Improve compliance and mitigate legal risks, wherever you do business.
Results you can measure
The number 1 expensing app in the market
GDPR compliant, ISO 27001 certified, SOC 2 Type 2 reported
Integrations
Connected with your favourite systems
Rydoo connects with over 35 Travel, HR, Finance, and ERP tools to enable full systems synchronisation
Customers
Don’t take our word for it, take theirs
Trusted by leaders and disrupters across 130+ countries
